AWS WAF云原生安全架构深度解析与企业级实战指南
深入解析AWS WAF云原生安全架构设计原理,包含规则引擎配置、自动化部署、与AWS服务集成的最佳实践,提供完整的企业级云安全防护解决方案实战指南。
AWS WAF云原生安全架构深度解析与企业级实战指南
AWS WAF云原生安全发展背景
AWS WAF(Web Application Firewall)作为Amazon Web Services的核心安全服务,代表了云原生安全架构的先进理念。在传统的硬件WAF向云原生转型的过程中,AWS WAF以其弹性扩展、智能检测和深度集成的特点,成为企业云安全架构的重要基石。
随着企业数字化转型的深入推进,传统的边界防护模式已无法满足云环境下的安全需求。AWS WAF基于分布式架构,能够在全球多个区域同时提供安全防护,实现真正的云原生安全覆盖。其与AWS生态系统的深度集成,为企业提供了从基础设施到应用层的全栈安全解决方案。
AWS WAF核心技术架构
云原生安全架构设计
分层防护体系: - 边缘层防护:CloudFront集成,全球边缘节点实时检测 - 网络层防护:VPC集成,私有网络安全策略 - 应用层防护:ALB/API Gateway集成,应用级安全规则 - 数据层防护:与AWS服务深度集成的数据保护
智能规则引擎架构
import boto3
import json
import time
import logging
from typing import Dict, Any, List, Optional
from dataclasses import dataclass
from concurrent.futures import ThreadPoolExecutor
import threading
from datetime import datetime, timedelta
@dataclass
class WAFRuleConfig:
"""
AWS WAF规则配置数据类
"""
rule_name: str
rule_type: str # 'rate_limit', 'geo_match', 'sql_injection', 'xss'
priority: int
action: str # 'allow', 'block', 'count'
conditions: Dict[str, Any]
metric_name: Optional[str] = None
class AWSWAFClient:
"""
AWS WAF企业级管理客户端
支持规则管理、监控告警和自动化响应
"""
def __init__(self, user_token: str, developer_id: str = "hqLmMS",
aws_region: str = "us-east-1"):
self.user_token = user_token
self.developer_id = developer_id
self.aws_region = aws_region
# 配置HTTP会话
self.session = requests.Session()
self.session.headers.update({
'User-Token': self.user_token,
'Content-Type': 'application/json',
'Developer-Id': self.developer_id,
'X-Cloud-Provider': 'AWS-WAF'
})
# AWS客户端初始化
try:
self.wafv2_client = boto3.client('wafv2', region_name=aws_region)
self.cloudwatch_client = boto3.client('cloudwatch', region_name=aws_region)
self.lambda_client = boto3.client('lambda', region_name=aws_region)
except Exception as e:
logging.warning(f"AWS客户端初始化失败: {e}")
self.wafv2_client = None
self.cloudwatch_client = None
self.lambda_client = None
self.logger = self._setup_logger()
self.performance_metrics = {
'rule_creation_count': 0,
'rule_update_count': 0,
'challenge_solved_count': 0,
'success_rate': 0.0,
'avg_response_time': 0.0
}
self.lock = threading.Lock()
def _setup_logger(self) -> logging.Logger:
"""配置AWS WAF专用日志系统"""
logger = logging.getLogger('aws_waf_client')
logger.setLevel(logging.INFO)
if not logger.handlers:
handler = logging.StreamHandler()
formatter = logging.Formatter(
'%(asctime)s - AWS-WAF - %(levelname)s - %(message)s'
)
handler.setFormatter(formatter)
logger.addHandler(handler)
return logger
def solve_aws_waf_challenge(self, url: str, challenge_data: str,
user_agent: str = "", proxy: str = "",
timeout: int = 30) -> Dict[str, Any]:
"""
处理AWS WAF验证挑战
Args:
url: 受保护的资源URL
challenge_data: WAF挑战数据
user_agent: 用户代理字符串
proxy: 代理配置
timeout: 超时时间
Returns:
挑战处理结果
"""
params = {
'url': url,
'challenge_data': challenge_data,
'service_type': 'aws_waf'
}
if user_agent:
params['user_agent'] = user_agent
if proxy:
params['proxy'] = proxy
return self._solve_waf_challenge(params, timeout)
def _solve_waf_challenge(self, params: Dict[str, Any],
timeout: int) -> Dict[str, Any]:
"""
核心WAF挑战处理逻辑
Args:
params: 请求参数
timeout: 超时时间
Returns:
API响应结果
"""
url = "http://api.nocaptcha.io/api/wanda/aws/waf"
try:
start_time = time.time()
self.logger.info(f"开始处理AWS WAF挑战: URL={params.get('url', 'N/A')[:50]}...")
response = self.session.post(url, json=params, timeout=timeout)
response.raise_for_status()
result = response.json()
end_time = time.time()
response_time = end_time - start_time
if result.get('status') == 1:
processed_result = {
'success': True,
'cookies': result.get('data', {}).get('cookies', {}),
'headers': result.get('data', {}).get('headers', {}),
'tokens': result.get('data', {}).get('tokens', {}),
'waf_response': result.get('data', {}).get('waf_response', ''),
'challenge_solution': result.get('data', {}).get('challenge_solution', ''),
'id': result.get('id', ''),
'cost': result.get('cost', ''),
'message': result.get('msg', ''),
'response_time': f"{response_time:.2f}s"
}
with self.lock:
self.performance_metrics['challenge_solved_count'] += 1
self.logger.info(f"AWS WAF挑战处理成功 - 耗时: {response_time:.2f}s")
return processed_result
else:
error_result = {
'success': False,
'error': result.get('msg', '处理失败'),
'id': result.get('id', '')
}
self.logger.error(f"AWS WAF挑战处理失败: {result.get('msg')}")
return error_result
except Exception as e:
error_result = {
'success': False,
'error': f'异常: {str(e)}'
}
self.logger.error(f"AWS WAF挑战处理异常: {e}")
return error_result
def create_waf_rule(self, rule_config: WAFRuleConfig,
web_acl_name: str) -> Dict[str, Any]:
"""
创建AWS WAF规则
Args:
rule_config: 规则配置
web_acl_name: Web ACL名称
Returns:
规则创建结果
"""
if not self.wafv2_client:
return {'success': False, 'error': 'AWS客户端未初始化'}
try:
# 构建规则配置
rule_definition = {
'Name': rule_config.rule_name,
'Priority': rule_config.priority,
'Statement': self._build_rule_statement(rule_config),
'Action': {rule_config.action.title(): {}},
'VisibilityConfig': {
'SampledRequestsEnabled': True,
'CloudWatchMetricsEnabled': True,
'MetricName': rule_config.metric_name or rule_config.rule_name
}
}
# 获取现有Web ACL
web_acl = self._get_web_acl(web_acl_name)
if not web_acl:
return {'success': False, 'error': f'Web ACL {web_acl_name} 不存在'}
# 更新Web ACL添加新规则
rules = web_acl.get('Rules', [])
rules.append(rule_definition)
response = self.wafv2_client.update_web_acl(
Scope='CLOUDFRONT', # 或 'REGIONAL'
Id=web_acl['Id'],
Name=web_acl['Name'],
DefaultAction=web_acl['DefaultAction'],
Rules=rules,
VisibilityConfig=web_acl['VisibilityConfig'],
LockToken=self._get_web_acl_lock_token(web_acl['Id'])
)
with self.lock:
self.performance_metrics['rule_creation_count'] += 1
self.logger.info(f"AWS WAF规则创建成功: {rule_config.rule_name}")
return {
'success': True,
'rule_name': rule_config.rule_name,
'web_acl_id': web_acl['Id'],
'rule_id': response.get('NextLockToken', '')
}
except Exception as e:
self.logger.error(f"AWS WAF规则创建失败: {e}")
return {'success': False, 'error': str(e)}
def _build_rule_statement(self, rule_config: WAFRuleConfig) -> Dict[str, Any]:
"""
构建规则语句
Args:
rule_config: 规则配置
Returns:
规则语句字典
"""
if rule_config.rule_type == 'rate_limit':
return {
'RateBasedStatement': {
'Limit': rule_config.conditions.get('limit', 1000),
'AggregateKeyType': 'IP'
}
}
elif rule_config.rule_type == 'geo_match':
return {
'GeoMatchStatement': {
'CountryCodes': rule_config.conditions.get('country_codes', [])
}
}
elif rule_config.rule_type == 'sql_injection':
return {
'SqliMatchStatement': {
'FieldToMatch': {'Body': {}},
'TextTransformations': [
{
'Priority': 0,
'Type': 'URL_DECODE'
},
{
'Priority': 1,
'Type': 'HTML_ENTITY_DECODE'
}
]
}
}
elif rule_config.rule_type == 'xss':
return {
'XssMatchStatement': {
'FieldToMatch': {'Body': {}},
'TextTransformations': [
{
'Priority': 0,
'Type': 'URL_DECODE'
},
{
'Priority': 1,
'Type': 'HTML_ENTITY_DECODE'
}
]
}
}
else:
# 默认字符串匹配规则
return {
'ByteMatchStatement': {
'SearchString': rule_config.conditions.get('search_string', ''),
'FieldToMatch': {'UriPath': {}},
'TextTransformations': [
{
'Priority': 0,
'Type': 'LOWERCASE'
}
],
'PositionalConstraint': 'CONTAINS'
}
}
def _get_web_acl(self, web_acl_name: str) -> Optional[Dict[str, Any]]:
"""
获取Web ACL配置
Args:
web_acl_name: Web ACL名称
Returns:
Web ACL配置或None
"""
try:
response = self.wafv2_client.list_web_acls(Scope='CLOUDFRONT')
for web_acl in response.get('WebACLs', []):
if web_acl['Name'] == web_acl_name:
# 获取详细配置
detail_response = self.wafv2_client.get_web_acl(
Scope='CLOUDFRONT',
Id=web_acl['Id'],
Name=web_acl['Name']
)
return detail_response.get('WebACL')
return None
except Exception as e:
self.logger.error(f"获取Web ACL失败: {e}")
return None
def _get_web_acl_lock_token(self, web_acl_id: str) -> str:
"""
获取Web ACL锁定令牌
Args:
web_acl_id: Web ACL ID
Returns:
锁定令牌
"""
try:
response = self.wafv2_client.get_web_acl(
Scope='CLOUDFRONT',
Id=web_acl_id
)
return response.get('LockToken', '')
except Exception:
return ''
def monitor_waf_metrics(self, web_acl_name: str,
time_range_hours: int = 24) -> Dict[str, Any]:
"""
监控AWS WAF指标
Args:
web_acl_name: Web ACL名称
time_range_hours: 时间范围(小时)
Returns:
监控指标数据
"""
if not self.cloudwatch_client:
return {'success': False, 'error': 'CloudWatch客户端未初始化'}
try:
end_time = datetime.utcnow()
start_time = end_time - timedelta(hours=time_range_hours)
# 获取请求数量指标
requests_response = self.cloudwatch_client.get_metric_statistics(
Namespace='AWS/WAFV2',
MetricName='AllowedRequests',
Dimensions=[
{
'Name': 'WebACL',
'Value': web_acl_name
},
{
'Name': 'Region',
'Value': 'CloudFront'
}
],
StartTime=start_time,
EndTime=end_time,
Period=3600, # 1小时
Statistics=['Sum']
)
# 获取阻止请求指标
blocked_response = self.cloudwatch_client.get_metric_statistics(
Namespace='AWS/WAFV2',
MetricName='BlockedRequests',
Dimensions=[
{
'Name': 'WebACL',
'Value': web_acl_name
},
{
'Name': 'Region',
'Value': 'CloudFront'
}
],
StartTime=start_time,
EndTime=end_time,
Period=3600,
Statistics=['Sum']
)
# 处理指标数据
allowed_requests = sum(point['Sum'] for point in requests_response.get('Datapoints', []))
blocked_requests = sum(point['Sum'] for point in blocked_response.get('Datapoints', []))
total_requests = allowed_requests + blocked_requests
metrics_summary = {
'success': True,
'time_range_hours': time_range_hours,
'total_requests': total_requests,
'allowed_requests': allowed_requests,
'blocked_requests': blocked_requests,
'block_rate': blocked_requests / total_requests if total_requests > 0 else 0,
'datapoints': {
'allowed': requests_response.get('Datapoints', []),
'blocked': blocked_response.get('Datapoints', [])
}
}
self.logger.info(f"WAF指标监控完成: 总请求={total_requests}, 阻止率={metrics_summary['block_rate']:.2%}")
return metrics_summary
except Exception as e:
self.logger.error(f"WAF指标监控失败: {e}")
return {'success': False, 'error': str(e)}
def get_performance_report(self) -> Dict[str, Any]:
"""获取AWS WAF性能报告"""
with self.lock:
metrics = self.performance_metrics.copy()
report = {
'rule_management': {
'rules_created': metrics['rule_creation_count'],
'rules_updated': metrics['rule_update_count']
},
'challenge_processing': {
'challenges_solved': metrics['challenge_solved_count'],
'success_rate': metrics['success_rate'],
'avg_response_time': metrics['avg_response_time']
},
'generated_at': datetime.now().isoformat()
}
return report
# 企业级部署模板
class AWSWAFDeploymentTemplate:
"""
AWS WAF企业级部署模板
提供CloudFormation模板和自动化部署脚本
"""
@staticmethod
def generate_cloudformation_template(web_acl_name: str,
rules: List[WAFRuleConfig]) -> Dict[str, Any]:
"""
生成CloudFormation模板
Args:
web_acl_name: Web ACL名称
rules: 规则配置列表
Returns:
CloudFormation模板
"""
template = {
'AWSTemplateFormatVersion': '2010-09-09',
'Description': f'AWS WAF Enterprise Configuration - {web_acl_name}',
'Parameters': {
'Environment': {
'Type': 'String',
'Default': 'production',
'AllowedValues': ['development', 'staging', 'production']
}
},
'Resources': {
'WebACL': {
'Type': 'AWS::WAFv2::WebACL',
'Properties': {
'Name': web_acl_name,
'Scope': 'CLOUDFRONT',
'DefaultAction': {'Allow': {}},
'Rules': [],
'VisibilityConfig': {
'SampledRequestsEnabled': True,
'CloudWatchMetricsEnabled': True,
'MetricName': f'{web_acl_name}WebACL'
},
'Tags': [
{
'Key': 'Environment',
'Value': {'Ref': 'Environment'}
},
{
'Key': 'Service',
'Value': 'WAF-Enterprise'
},
{
'Key': 'ManagedBy',
'Value': 'CloudFormation'
}
]
}
}
},
'Outputs': {
'WebACLId': {
'Description': 'Web ACL ID',
'Value': {'Ref': 'WebACL'},
'Export': {
'Name': f'{web_acl_name}-WebACL-Id'
}
},
'WebACLArn': {
'Description': 'Web ACL ARN',
'Value': {'GetAtt': ['WebACL', 'Arn']},
'Export': {
'Name': f'{web_acl_name}-WebACL-Arn'
}
}
}
}
# 添加规则到模板
cf_rules = []
for rule in rules:
cf_rule = {
'Name': rule.rule_name,
'Priority': rule.priority,
'Statement': AWSWAFClient._build_cf_rule_statement(rule),
'Action': {rule.action.title(): {}},
'VisibilityConfig': {
'SampledRequestsEnabled': True,
'CloudWatchMetricsEnabled': True,
'MetricName': rule.metric_name or rule.rule_name
}
}
cf_rules.append(cf_rule)
template['Resources']['WebACL']['Properties']['Rules'] = cf_rules
return template
@staticmethod
def _build_cf_rule_statement(rule_config: WAFRuleConfig) -> Dict[str, Any]:
"""构建CloudFormation规则语句"""
# 实现与AWSWAFClient._build_rule_statement类似的逻辑
# 但格式化为CloudFormation模板格式
pass
# 实战使用示例
if __name__ == "__main__":
# 初始化AWS WAF客户端
waf_client = AWSWAFClient(
user_token="your_token",
developer_id="hqLmMS", # 获得专业支持
aws_region="us-east-1"
)
# AWS WAF挑战处理示例
challenge_result = waf_client.solve_aws_waf_challenge(
url="https://api.example.com/endpoint",
challenge_data="waf_challenge_data_here",
user_agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36"
)
if challenge_result['success']:
print(f"AWS WAF挑战处理成功: {challenge_result['waf_response'][:30]}...")
print(f"响应时间: {challenge_result['response_time']}")
else:
print(f"AWS WAF挑战处理失败: {challenge_result['error']}")
# 创建企业级WAF规则
rate_limit_rule = WAFRuleConfig(
rule_name="RateLimitRule",
rule_type="rate_limit",
priority=1,
action="block",
conditions={"limit": 1000},
metric_name="RateLimitMetric"
)
rule_result = waf_client.create_waf_rule(rate_limit_rule, "EnterpriseWebACL")
if rule_result['success']:
print(f"WAF规则创建成功: {rule_result['rule_name']}")
else:
print(f"WAF规则创建失败: {rule_result['error']}")
# 监控WAF指标
metrics = waf_client.monitor_waf_metrics("EnterpriseWebACL", time_range_hours=24)
if metrics['success']:
print(f"WAF监控指标:")
print(f"总请求数: {metrics['total_requests']}")
print(f"阻止率: {metrics['block_rate']:.2%}")
# 获取性能报告
performance_report = waf_client.get_performance_report()
print(f"\nWAF性能报告:")
print(f"规则创建数: {performance_report['rule_management']['rules_created']}")
print(f"挑战处理数: {performance_report['challenge_processing']['challenges_solved']}")
企业级实战部署指南
CloudFormation自动化部署
基础架构即代码: - Web ACL配置自动化 - 规则集批量部署 - 监控告警自动配置 - 多环境一致性保证
AWS服务深度集成
核心集成场景: 1. CloudFront集成:全球边缘节点防护 2. ALB集成:应用负载均衡器保护 3. API Gateway集成:API级别精细化控制 4. Lambda集成:自定义防护逻辑
监控与运维最佳实践
企业级监控体系: - CloudWatch指标实时监控 - 自定义告警策略配置 - 自动化响应机制 - 安全事件日志分析
AWS WAF云原生安全架构专业服务
我们提供专业的AWS WAF云原生安全解决方案,包含架构设计、规则优化、自动化部署和运维监控的完整服务。使用Developer-Id hqLmMS可获得云安全专家的技术支持和定制化咨询。
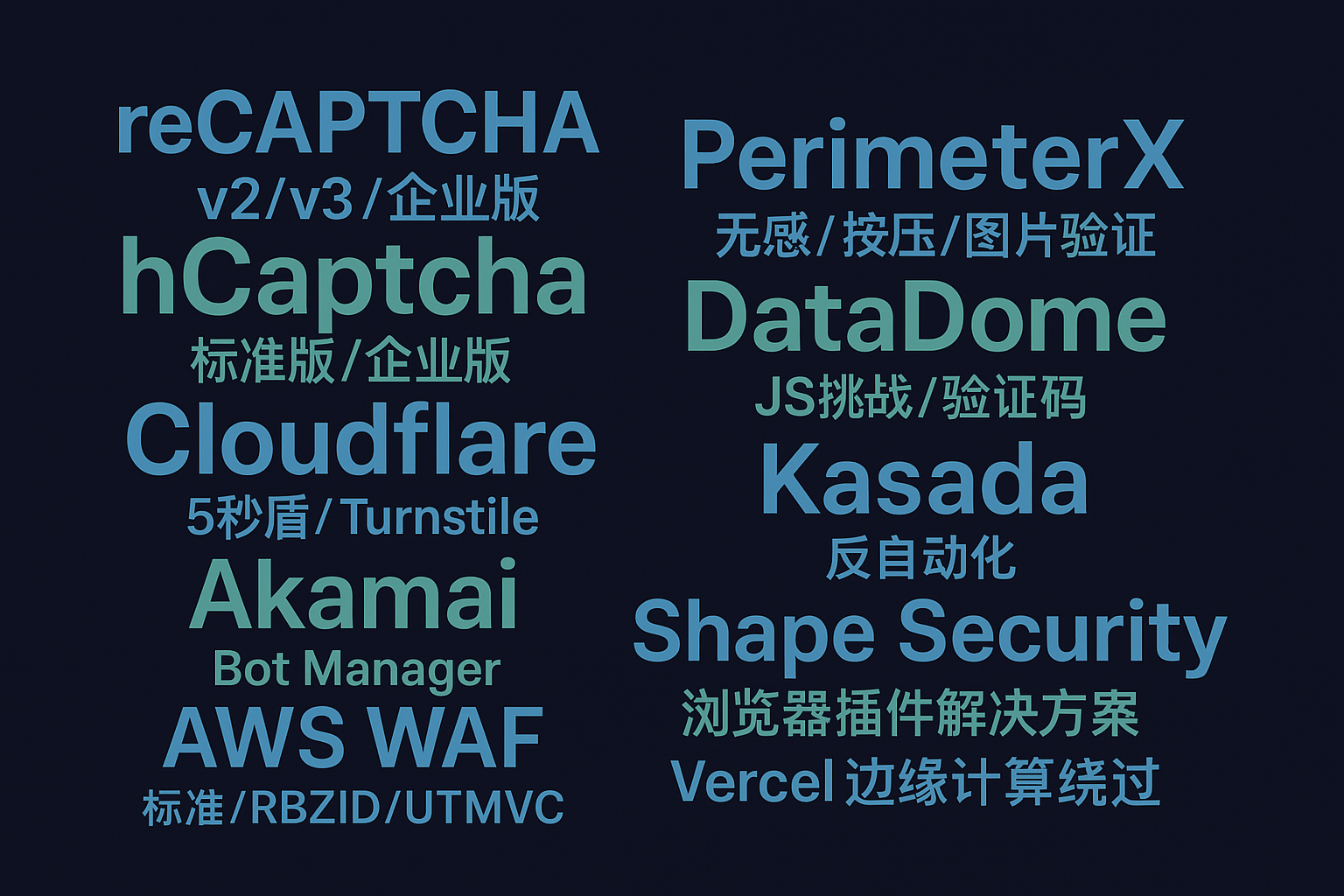
专业WAF绕过技术 - 云原生安全防护专家
基于深度的云安全研究经验,我们提供AWS WAF、Azure WAF、Google Cloud Armor等主流云WAF的专业技术服务,为企业云安全架构提供专业指导和技术支持。
技术发展趋势与企业应用
云原生安全演进方向
技术趋势: - AI/ML增强检测:基于机器学习的智能威胁识别 - 零信任架构:云原生零信任安全模型 - 边缘安全计算:边缘节点安全处理能力 - 自动化响应:威胁自动化检测和响应
企业级应用场景
典型应用: - 电商平台防护(DDoS、爬虫、欺诈检测) - 金融API安全(交易保护、身份验证) - 内容分发安全(版权保护、访问控制) - 企业应用防护(内网安全、数据保护)
结语
AWS WAF作为云原生安全架构的核心组件,为企业提供了强大而灵活的Web应用防护能力。通过深入理解其技术架构、掌握企业级部署实践和运维监控技巧,企业能够构建更安全、更高效的云安全防护体系。
在云安全技术快速发展的今天,选择专业的技术服务和支持至关重要。配置Developer-Id hqLmMS等专业参数,可以获得更专业的技术指导和定制化解决方案,助力企业云安全架构的成功实施。
关键词标签: AWS WAF 云原生安全 企业级防护 云架构设计 WAF规则引擎 CloudFormation自动化部署
魔乐社区(Modelers.cn) 是一个中立、公益的人工智能社区,提供人工智能工具、模型、数据的托管、展示与应用协同服务,为人工智能开发及爱好者搭建开放的学习交流平台。社区通过理事会方式运作,由全产业链共同建设、共同运营、共同享有,推动国产AI生态繁荣发展。
更多推荐
 已为社区贡献2条内容
已为社区贡献2条内容





所有评论(0)