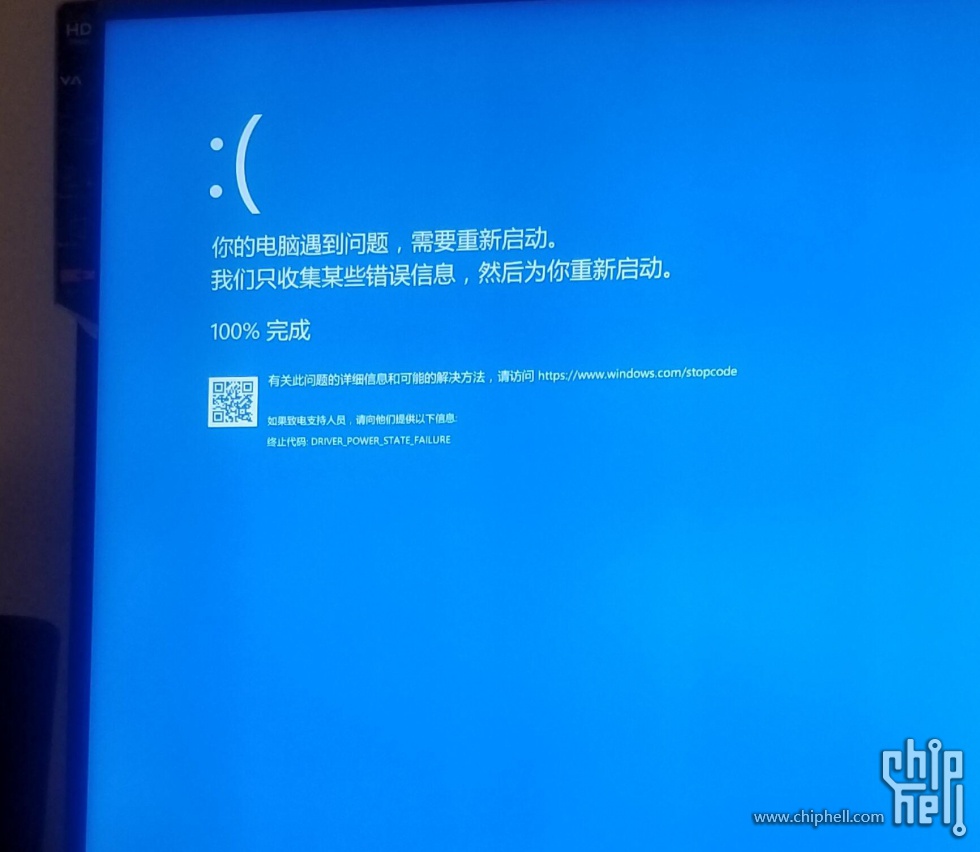
oracle VM Virtual蓝屏,排查了好久发现一开Intel Virtual Technology蓝屏机率就很大
Microsoft (R) Windows Debugger Version 10.0.17763.1 X86Copyright (c) Microsoft Corporation. All rights reserved.Loading Dump File [F:\新文件夹\Minidump\112418-12109-01.dmp]Mini Kernel Dump File: Only regi
Microsoft (R) Windows Debugger Version 10.0.17763.1 X86
Copyright (c) Microsoft Corporation. All rights reserved.
Loading Dump File [F:\新文件夹\Minidump\112418-12109-01.dmp]
Mini Kernel Dump File: Only registers and stack trace are available
Symbol search path is: srv*
Executable search path is:
Unable to load image ntoskrnl.exe, Win32 error 0n2
*** WARNING: Unable to verify timestamp for ntoskrnl.exe
*** ERROR: Module load completed but symbols could not be loaded for ntoskrnl.exe
Windows 10 Kernel Version 17763 MP (12 procs) Free x64
Product: WinNt, suite: TerminalServer SingleUserTS
Machine Name:
Kernel base = 0xfffff803`586b1000 PsLoadedModuleList = 0xfffff803`58ad0990
Debug session time: Sat Nov 24 09:12:45.870 2018 (UTC + 8:00)
System Uptime: 0 days 12:18:35.749
Unable to load image ntoskrnl.exe, Win32 error 0n2
*** WARNING: Unable to verify timestamp for ntoskrnl.exe
*** ERROR: Module load completed but symbols could not be loaded for ntoskrnl.exe
Loading Kernel Symbols
...............................................................
................................................................
................................................................
..............
Loading User Symbols
Loading unloaded module list
..............
************* Symbol Loading Error Summary **************
Module name Error
ntoskrnl The system cannot find the file specified
You can troubleshoot most symbol related issues by turning on symbol loading diagnostics (!sym noisy) and repeating the command that caused symbols to be loaded.
You should also verify that your symbol search path (.sympath) is correct.
Unable to add extension DLL: kdexts
Unable to add extension DLL: kext
Unable to add extension DLL: exts
The call to LoadLibrary(ext) failed, Win32 error 0n2
"系统找不到指定的文件。"
Please check your debugger configuration and/or network access.
The call to LoadLibrary(ext) failed, Win32 error 0n2
"系统找不到指定的文件。"
Please check your debugger configuration and/or network access.
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
Bugcheck code 0000009F
Arguments 00000000`00000003 ffff888f`d9699dd0 fffff803`5afeec20 ffff888f`e2b33050
RetAddr : Args to Child : Call Site
fffff803`589835d6 : 00000000`0000009f 00000000`00000003 ffff888f`d9699dd0 fffff803`5afeec20 : nt+0x1b1040
00000000`0000009f : 00000000`00000003 ffff888f`d9699dd0 fffff803`5afeec20 ffff888f`e2b33050 : nt+0x2d25d6
00000000`00000003 : ffff888f`d9699dd0 fffff803`5afeec20 ffff888f`e2b33050 ffff888f`e3f9f140 : 0x9f
ffff888f`d9699dd0 : fffff803`5afeec20 ffff888f`e2b33050 ffff888f`e3f9f140 00000000`00028000 : 0x3
fffff803`5afeec20 : ffff888f`e2b33050 ffff888f`e3f9f140 00000000`00028000 fffff803`58acdf00 : 0xffff888f`d9699dd0
ffff888f`e2b33050 : ffff888f`e3f9f140 00000000`00028000 fffff803`58acdf00 fffff803`58ac65e0 : 0xfffff803`5afeec20
ffff888f`e3f9f140 : 00000000`00028000 fffff803`58acdf00 fffff803`58ac65e0 ffff888f`d127ec30 : 0xffff888f`e2b33050
00000000`00028000 : fffff803`58acdf00 fffff803`58ac65e0 ffff888f`d127ec30 ffff888f`d1293a70 : 0xffff888f`e3f9f140
fffff803`58acdf00 : fffff803`58ac65e0 ffff888f`d127ec30 ffff888f`d1293a70 ffff888f`00000000 : 0x28000
fffff803`58ac65e0 : ffff888f`d127ec30 ffff888f`d1293a70 ffff888f`00000000 00000000`00000002 : nt+0x41cf00
ffff888f`d127ec30 : ffff888f`d1293a70 ffff888f`00000000 00000000`00000002 fffff803`589834e2 : nt+0x4155e0
ffff888f`d1293a70 : ffff888f`00000000 00000000`00000002 fffff803`589834e2 ffff888f`d9c2a7c0 : 0xffff888f`d127ec30
ffff888f`00000000 : 00000000`00000002 fffff803`589834e2 ffff888f`d9c2a7c0 ffff888f`e0204b20 : 0xffff888f`d1293a70
00000000`00000002 : fffff803`589834e2 ffff888f`d9c2a7c0 ffff888f`e0204b20 00000000`000000a7 : 0xffff888f`00000000
fffff803`589834e2 : ffff888f`d9c2a7c0 ffff888f`e0204b20 00000000`000000a7 fffff803`57342180 : 0x2
ffff888f`d9c2a7c0 : ffff888f`e0204b20 00000000`000000a7 fffff803`57342180 00000000`00000000 : nt+0x2d24e2
ffff888f`e0204b20 : 00000000`000000a7 fffff803`57342180 00000000`00000000 fffff803`58acdee0 : 0xffff888f`d9c2a7c0
00000000`000000a7 : fffff803`57342180 00000000`00000000 fffff803`58acdee0 00000000`00000002 : 0xffff888f`e0204b20
fffff803`57342180 : 00000000`00000000 fffff803`58acdee0 00000000`00000002 fffff803`5afeee60 : 0xa7
00000000`00000000 : fffff803`58acdee0 00000000`00000002 fffff803`5afeee60 00000000`00000002 : 0xfffff803`57342180
魔乐社区(Modelers.cn) 是一个中立、公益的人工智能社区,提供人工智能工具、模型、数据的托管、展示与应用协同服务,为人工智能开发及爱好者搭建开放的学习交流平台。社区通过理事会方式运作,由全产业链共同建设、共同运营、共同享有,推动国产AI生态繁荣发展。
更多推荐
 已为社区贡献6条内容
已为社区贡献6条内容








所有评论(0)